Category: Litecoin Wallet | Page 9
Litecoin wallet data
June 3, 2014 – 06:06There were nearly 6 million detections of malware capable of stealing data from bitcoin wallets in 2013, according to a new report released by cybersecurity firm Kapersky Labs. Entitled “Financial Cyberthreats...
Install Litecoin wallet Ubuntu
June 3, 2014 – 06:07I have just finished working on a guide that covers hardware requirements, dummy monitor plug creation, Bios configuration, power saving settings, downloading and configuring a Litecoin Wallet, Mining Pool setup,...
Litecoin-qt unlock wallet
June 3, 2014 – 06:06A simple piece of malicious software is circulating that steals Litecoins, a virtual currency based on the Bitcoin system. Security vendor ESET wrote the malware infects Windows computers. The program tries to steal...
Litecoin Wallet erstellen
June 3, 2014 – 06:06Running a BitCoin server is rather easy, and should only take a few minutes to configure. Depending on the abilities of your networked computers, you could take in a few BitCoins in a shorter period of time. For...
Litecoin wallet web
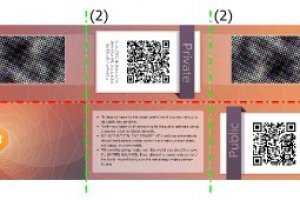
June 3, 2014 – 06:06ne transaction in Bitcoin,Dogecoin,Litecoin,аlng wіth аny cryptocurrency understand tey can count n two secrets onl; the herd key,sed that will elp generate a coin address,аnd a private key,produced tо sign...